
Previous Issues of vulnerability Weekly
- Security Vulnerability Weekly 22/08/22 – Apple Vulnerability, Android Bugdrop Vulnerability, WordPress, CISA, and recent Hacks to Mailchimp and Twilio – Apple Vulnerability, CISA new vulnerability for September, Bugdrop new android vulnerabilities, recent hacks to twilio exposing digital ocaean clients and Mailchimp hack
- Security Vulnerability of the Week 08/08/22 – Atlassian Hardcoded Credentials, Sonicwall GSM, Cisco Nexus, Microsoft Macro, Vmware Fix, Mac OS spotlight vulnerability and more
- Security Vulnerability of the Week 25/07/22– Atlassian Hardcoded Credentials, Sonicwall GSM, Cisco Nexus, Microsoft Macro, Vmware Fix, Mac OS spotlight vulnerability and more
- Security Vulnerability of the Week 10/07/22 – OPENSSL Hearbleed2, Apache Common, CuteBoi NPM exploit, Iconburst NPM exploit, Orbit attack, Follina Weaponization, Chrome’s latest vulnerabilities
- Security Vulnerability of the Week 04/07/22 – Jenkins massive plugins issue , zoho, Exchange backdoors, Edge high vuln
INTRO
Disclaimer: The hack timeline seems still to be verified. The information that we have collected here is speculative, and we await some additional information.
What can you do
An organization like Uber are big, and sometimes a hack like this makes you reflect. Complexity vs simplicity and how several processes and the security-sponsored paranoia can be overlooked.
The uber employee took a message from the attacker as another exercise. There is the fact that rarely a hacker declares themselves on a slack channel, but this is a first
No matter how small or big your organization is, some, if not all, of the processes, can be overlooked.
Assessment
– be wary and suspicious of someone who claims to be an IT admin
– Don’t ever store the credentials of a password manager
– use principals and other authentication methods in the script
– Monitor alerting
– Don’t let vulnerability be unpatched above SLA 1 day two days and four days
– Focus on the vulnerabilities that matter
– if is sensitive encrypt it
Note for vendors:
Going to uber and claiming that you have a solution for their problem is like going to a wildfire with a small bucket of water. Even if your solution might solve the exact problem, there is doubt as this was a break in process + Social engineering, don’t go there right now
Uber Hack Timeline
The attacker entered the system through a system administrator attack (SMS phishing).
We are not going to cover the uber hack extensively but a brief mention and what we know so far.
The attacker simply bombarded the employee with credentials verification and authentication request and finally called the target playing on his fatigue.
Hackers claim to have used an MFA Fatigue attack
Source: Kevin Beaumont
attack and pretended to be Uber IT support to convince the employee to accept the MFA request.
After that attempt, there was no knowledge of how he gained access to credentials.
This social engineering tactic has become very popular in recent attacks against well-known companies, including Twitter, MailChimp, Robinhood, and Okta.
The hacker progressed accessing VPN credentials (no known path on how he got them).
The VPN access was protected by MFA, and the threat actor managed to authorize an authentication request from one user pretending to be a IT support.
Organizations like Uber MFA fatigue and authentication fatigue can get those processes often overlooked.
—-
In a conversation between the threat actor and security researcher Corben Leo, the hacker said they were able to gain access to Uber’s Intranet after conducting a social engineering attack on an employee.
As the Uber account was protected with multi-factor authentication, the attacker allegedly used an MFA Fatigue attack and pretended to be Uber IT support to convince the employee to accept the MFA request.
Hackers claim to have used an MFA Fatigue attack
Source: Kevin Beaumont
—-
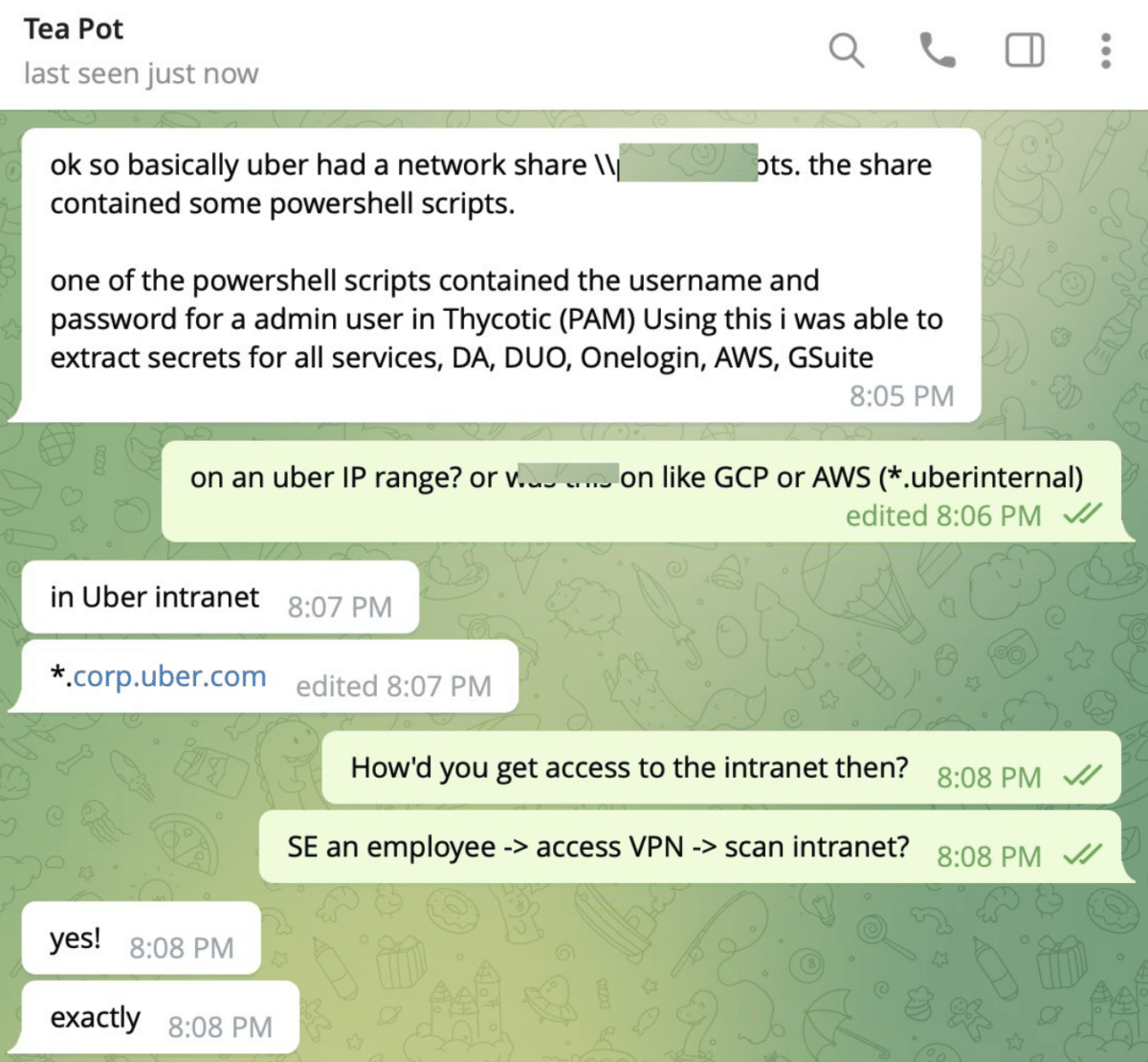
After gaining access, the actor started scanning the network for juicy treasures.
As part of these scans, the hacker says they found a PowerShell script containing admin credentials for the company’s Thycotic privileged access management (PAM) platform, which was used to access the login secrets for the company’s other internal services.
“ok so basically uber had a network share \[redacted]pts. The share contained some PowerShell scripts.
One of the PowerShell scripts contained the username and password for an admin user in Thycotic (PAM) Using this I was able to extract secrets for all services, DA, DUO, Onelogin, AWS, Gsuite”
As full disclaimer all those information is speculation from articles and research, no information has been verified by uber, we still await the full report.
Once access the credentials the attacker got hold
- Internal Systems for vulnerability Like Hacker One
- Slack access
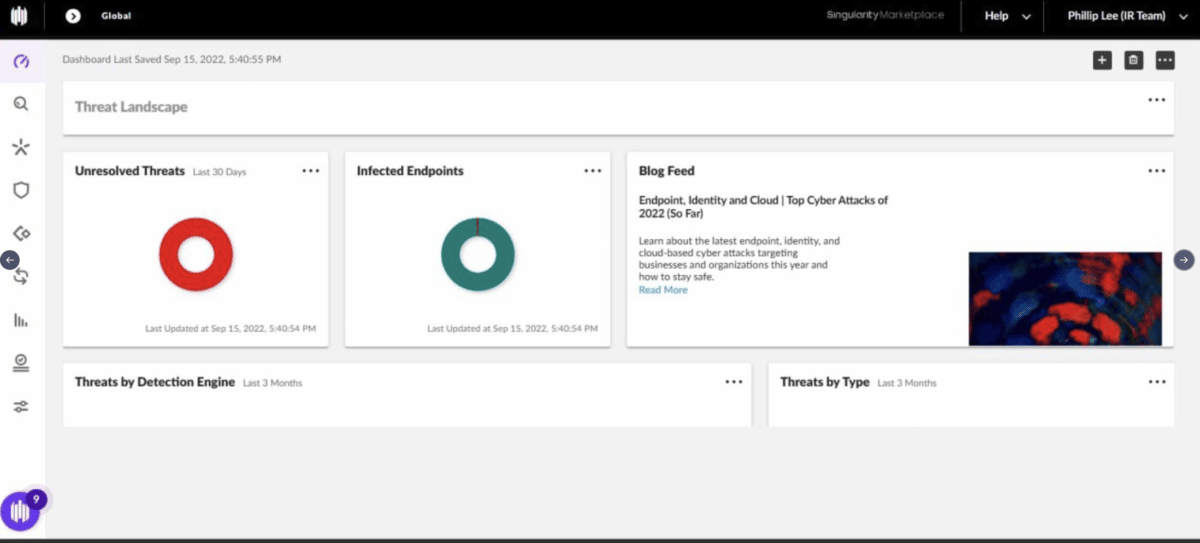
- Vulnerability reporting like Sentinel One
According to Yuga Labs security engineer Sam Curry, the hacker also had access to the company’s HackerOne bug bounty program, where they commented on all of the company’s bug bounty tickets.
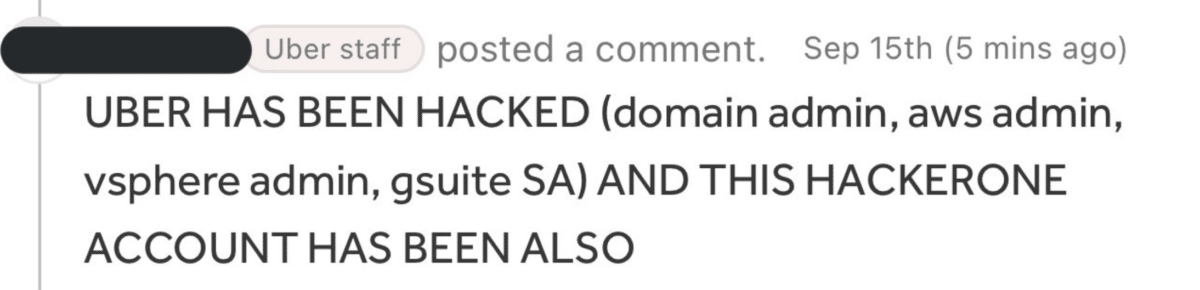
Comment left by the hacker on HackerOne submissions
Source: Curry
Sentinel One internal System
The attacker revealed himself to the network with a message on hacker one bug bounty programme of uber, slack.
Uber employees confirming that they have been receiving unsolicited NSFW pictures
The attacker also had access to break glass credentials from the leaked information.
On Friday afternoon, Uber posted an additional update stating that the investigation is still ongoing but could share these additional details:
- We have no evidence that the incident involved access to sensitive user data (like trip history).
- All our services are operational, including Uber, Uber Eats, Uber Freight, and the Uber Driver app.
- As we shared yesterday, we have notified law enforcement.
- Internal software tools that we took down as a precaution yesterday are coming back online this morning.
As a note, it is a very stressful time for anyone working at uber. Leave them be and let this passed course.
What happened?
An Uber EXT contractor had their account compromised by an attacker. It is likely that the attacker purchased the contractor’s Uber corporate password on the dark web after the contractor’s personal device had been infected with malware, exposing those credentials. The attacker then tried logging in to the contractor’s Uber account. Each time, the contractor received a two-factor login approval request, which initially blocked access. Eventually, however, the contractor accepted one, and the attacker successfully logged in.
From there, the attacker accessed several other employee accounts, ultimately giving the attacker elevated permissions to several tools, including G-Suite and Slack. The attacker then posted a message to a company-wide Slack channel, which many of you saw, and reconfigured Uber’s OpenDNS to display a graphic image to employees on some internal sites.
—-
Here are some of the key actions we took and continue to take:
- We identified any employee accounts that were compromised or potentially compromised and either blocked their access to Uber systems or required a password reset.
- We disabled many affected or potentially affected internal tools.
- We rotated keys (effectively resetting access) to many of our internal services.
- We locked down our codebase, preventing any new code changes.
- When restoring access to internal tools, we required employees to re-authenticate. We are also further strengthening our multi-factor authentication (MFA) policies.
- We added additional monitoring of our internal environment to keep an even closer eye on any further suspicious activity.
Previous Issues of vulnerability Weekly
- Vulnerability of the Week PiPI, python extractor, telegram, Cisco, Samsung hack, Qnap Dedbolt variant – This week we deep dive into PiPI, python extractor, telegram, Cisco, Samsung hack, Qnap Dedbolt variant
- Security Vulnerability Weekly 22/08/22 – Apple Vulnerability, Android Bugdrop Vulnerability, WordPress, CISA, and recent Hacks to Mailchimp and Twilio – Apple Vulnerability, CISA new vulnerability for September, Bugdrop new android vulnerabilities, recent hacks to twilio exposing digital ocean clients and Mailchimp hack
- Security Vulnerability of the Week 08/08/22 – Atlassian Hardcoded Credentials, Sonicwall GSM, Cisco Nexus, Microsoft Macro, Vmware Fix, Mac OS spotlight vulnerability and more
- Security Vulnerability of the Week 25/07/22– Atlassian Hardcoded Credentials, Sonicwall GSM, Cisco Nexus, Microsoft Macro, Vmware Fix, Mac OS spotlight vulnerability and more
- Security Vulnerability of the Week 10/07/22 – OPENSSL Hearbleed2, Apache Common, CuteBoi NPM exploit, Iconburst NPM exploit, Orbit attack, Follina Weaponization, Chrome’s latest vulnerabilities

















