Join our Mailing list!
Get all the latest news, exclusive deals, and feature updates.
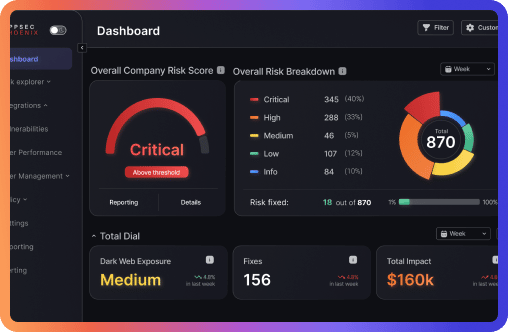
Asset management has always been a complex territory within the enterprises of today. Organizations with dynamic environments experience numerous challenges which make it difficult to have complete visibility over their network. With Phoenix Security Asset Management, regain control over your application security and cloud security environments.






Which vulnerability should i prioritize first? It’s a typical question asked by many overwhelmed security professionals.
How can organizations achieve more with less teams? Automating resolution and assigning tasks to the team. By streamlining these processes, teams can focus on the most critical risks, enhancing both vulnerability management and overall application security posture. This allows organizations to mitigate threats more efficiently, even with smaller security teams.
Laser focus on the top 10% of vulnerabilities that matter most today. Reduce risk faster with priority to contextualized vulnerabilities
Achieve a single view on vulnerabilities that are contextualized and prioritized. Reduce false positives.
Automatic threat intelligence identifies risk and improves efficiency, enabling fast reaction.
Accelerate security’s teams from triage and remove false positives.
Phoenix Security aggregates and automatically builds risk-based asset registers for cloud assets and application assets, providing continuous security assessment. Leverage powerful automation as the Phoenix Platform detects external and internal assets, proactively tackling vulnerabilities management and posture changes. With insights based on threat intelligence, you can effectively strengthen your cloud and application security posture.

Phoenix Security integrates natively with modern workflow and communication tools to provide engineers with all the information they need to solve vulnerabilities in real-time, whilst providing a real-time risk score of the business’ overall security posture.

Leverage Phoenix Security AppSec and CloudSec Knowledge Graph to track team association to application and assets. Leverage auto-tracking functionalities to understand who owns which assets and uncover the biggest risks from a team perspective.
Streamline vulnerability management by providing clear visibility into who is responsible for which assets, allowing teams to prioritize and address the most critical threats. Strengthen your application security posture and cloud security posture by empowering your security teams with the insights to manage risks effectively with Phoenix.

Security is a board-level issue. I need to provide my security team with the tools to do their job with brutal efficiency, minimizing the risk to the business.
When there are thousands of vulnerabilities, what I really need from the security team is a clear list of what to focus on. When everything is a priority, nothing is.

For appsec and DevSecOps teams. Prioritize appsec vulnerabilities and scale application security programs with risk-based approach

Prioritize Cloud misconfiguration and scale Cloud security programs with risk-based approach

ACT fast on Risk and fix the vulnerabilities and misconfigurations that matter most. Drive Risk based actions and set targets for engineers based on risk profile.

For SOC and SecOps teams. Prioritize vulnerability and scale vulnerability management programs with risk-based approach

Know the asset that you own, what’s assessed and act fast on the vulnerabilities that matter most. Asset management and risk assessment all in one.

Phoenix Securityempowers security teams to act fast on exploited vulnerabilities and when threat actors exploit them in the wild. Automate Ticket opening, escalation and block vulnerabiliites going to production.

Cloud Security Posture Management- correlate application security and Cloud security in one single place, allowing you to control and act on the most important misconfigurations

Application security posture management -automates the identification of software assets as well as the tracking and scheduling of all application security tools and processes
As a cyber security practitioner, I saw first-hand what complexity can do to an organization; risk has been the key to master and communicating with the business. I’ve seen it first hand in my years in cybersecurity.
Mike Takla
Co-Founder & Chief Revenue Officer at HackNotice

As both a deep practitioner of cloud and application security as well as cyber risk quantification, I am excited about the increased context and democratization of CRQ that Phoenix Security brings to the industry. There is not another platform looking to combine across disjointed security silos and also bring in a whole host of integrations, intelligence and quantification to the masse.
Jonathan Rau
CISO Lightspin, Former AWS Security

As cyber security practitioner I saw first had what problem application and operational security have and Phoenix Security is revolutionizing the way those two team communicate in terms of risk
Vandana Verma
Security Relationship Leader Snyk

As a cyber security practitioner, I saw first-hand what benefits centralizing and translating vulnerabilities volumetrics into cyber risk does
Chris Martorella
Product Security MIRO,Former CISO Skyscanner

As Appsec practitioner I saw first had what complexity does to an application and cloud security program. Phoenix Security understands how to execute at-scale cloud security and application security programs, linking applications to deployment. I am excited to see innovation that helps to simplify, visualize and prioritize
John Kinsella
Co-Founder Cysense Journey

Phoenix Security has a unique view on risk and quantification and is what we need in running application security programmes in an optimized way
Chris Hodson
CISO Contentful

DevSecOps programs are struggling to keep up with the sheer number of vulnerabilities across multiple build pipelines. Phoenix allows us to focus on the exploitable items first
Chris Romeo
Co-Founder Security Journey

Phoenix Security is solving an important problem in Application Security providing both high level risk based views for leadership, and detailed technical views for developers and engineers; and ultimately removing the friction running AppSec Programmes
Kevin Fielder
FNZ

I’ve seen Phoenix Security over the years and has one of the most compelling AppSec feature the prioritization of work for DevOps Team reducing the burden of work for resource-starved Security teams.
Stephen Owen
CISO Esure Group












Derek Fisher – Head of product security at a global fintech. Speaker, instructor, and author in application security.
Derek is an award winning author of a children’s book series in cybersecurity as well as the author of “The Application Security Handbook.” He is a university instructor at Temple University where he teaches software development security to undergraduate and graduate students. He is a speaker on topics in the cybersecurity space and has led teams, large and small, at organizations in the healthcare and financial industries. He has built and matured information security teams as well as implemented organizational information security strategies to reduce the organizations risk.
Derek got his start in the hardware engineering space where he learned about designing circuits and building assemblies for commercial and military applications. He later pursued a computer science degree in order to advance a career in software development. This is where Derek was introduced to cybersecurity and soon caught the bug. He found a mentor to help him grow in cybersecurity and then pursued a graduate degree in the subject.
Since then Derek has worked in the product security space as an architect and leader. He has led teams to deliver more secure software in organizations from multiple industries. His focus has been to raise the security awareness of the engineering organization while maintaining a practice of secure code development, delivery, and operations.
In his role, Jeevan handles a range of tasks, from architecting security solutions to collaborating with Engineering Leadership to address security vulnerabilities at scale and embed security into the fabric of the organization.

Jeevan Singh is the Director of Security Engineering at Rippling, with a background spanning various Engineering and Security leadership roles over the course of his career. He’s dedicated to the integration of security practices into software development, working to create a security-aware culture within organizations and imparting security best practices to the team.
In his role, Jeevan handles a range of tasks, from architecting security solutions to collaborating with Engineering Leadership to address security vulnerabilities at scale and embed security into the fabric of the organization.

James Berthoty has over ten years of experience across product and security domains. He founded Latio Tech to help companies find the right security tools for their needs without vendor bias.


Chris Romeo is a leading voice and thinker in application security, threat modeling, and security champions and the CEO of Devici and General Partner at Kerr Ventures. Chris hosts the award-winning “Application Security Podcast,” “The Security Table,” and “The Threat Modeling Podcast” and is a highly rated industry speaker and trainer, featured at the RSA Conference, the AppSec Village @ DefCon, OWASP Global AppSec, ISC2 Security Congress, InfoSec World and All Day DevOps. Chris founded Security Journey, a security education company, leading to an exit in 2022. Chris was the Chief Security Advocate at Cisco, spreading security knowledge through education and champion programs. Chris has twenty-six years of security experience, holding positions across the gamut, including application security, security engineering, incident response, and various Executive roles. Chris holds the CISSP and CSSLP certifications.

Jim Manico is the founder of Manicode Security, where he trains software developers on secure coding and security engineering. Jim is also the founder of Brakeman Security, Inc. and an investor/advisor for Signal Sciences. He is the author of Iron-Clad Java: Building Secure Web Applications (McGraw-Hill), a frequent speaker on secure software practices, and a member of the JavaOne Rockstar speaker community. Jim is also a volunteer for and former board member of the OWASP foundation.
Get all the latest news, exclusive deals, and feature updates.
