Weekly review of the top vulnerability issues of the week

This week there were mostly updates on existing flaws – Qnap, F5 discloses vulnerabilities,
This week features Apple O/S Zero Day, Cisco, and Netgear update, Zyxel Firewall, Sonicwall Patch, Nvidia add by CISA, the Russian attack on Italy during Eurovision, Eternity project
Appsec
Nothing Major this week on application security or packages
INFRA/Network
Apple OS AVD

Patch has been released
Named CVE-2022-22675 in the AppleAVD (a kernel extension for audio and video decoding) that allows apps to execute arbitrary code with kernel privileges.
Details: https://support.apple.com/en-us/HT213220
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Apple macOS. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the AppleScript framework. Crafted data in a SCPT file can trigger a read past the end of an allocated data structure. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process.
Credit: Mickey Jin (@patch1t) of Trend Micro
The bug was reported by anonymous researchers and fixed by Apple in macOS Big Sur 11.6., watchOS 8.6, and tvOS 15.5 with improved bounds checking.
The list of impacted devices includes Apple Watch Series 3 or late, Macs running macOS Big Sur, Apple TV 4K, Apple TV 4K (2nd generation), and Apple TV HD.
This year there have been 5 security updates on apple
QNAP
QNAP Has released OS Firmware for the following vulnerabilities Tracked as
CVE-2022-23121 and others were discovered by NCC Group EDG team at Pwn2Own
The following Vulnerabilities were patched in the latest release
- CVE-2022-27588 (CVSS score: 9.8), the vulnerability has been addressed in QVR 5.1.6 build 20220401 and later.
- CVE-2021-38693 (CVSS score: 5.3) – A path traversal vulnerability in the httpd affecting QNAP devices running QTS, QuTS hero, QuTScloud, and QVR Pro Appliance, leading to information disclosure
- CVE-2021-44051 (CVSS score: 8.8) – A command injection vulnerability in QNAP devices running QTS, QuTS hero, and QuTScloud, resulting in arbitrary command execution
- CVE-2021-44052 (CVSS score: 6.5) – An improper link resolution before file access (“link following”) vulnerability in QNAP devices running QTS, QuTS hero, and QuTScloud, allowing attackers to read/write files in arbitrary file locations
- CVE-2021-44053 (CVSS score: 5.7) – A cross-site scripting (XSS) vulnerability in QNAP devices running QTS, QuTS hero, and QuTScloud, leading to code injection
- CVE-2021-44054 (CVSS score: 4.3) – An open redirect vulnerability in QNAP devices running QTS, QuTS hero, and QuTScloud, making it possible to redirect users to a rogue web pages
- CVE-2021-44055 (CVSS score: 5.3) – A missing authorization vulnerability in QNAP devices running Video Station, allowing attackers to access data or perform unauthorized actions
- CVE-2021-44056 (CVSS score: 7.1) – An improper authentication vulnerability in QNAP devices running Video Station, leading to system compromise
- CVE-2021-44057 (CVSS score: 7.1) – An improper authentication vulnerability in QNAP devices running Photo Station, leading to system compromise
More details: https://www.qnap.com/en-uk/securitydvisories
Affected Versions
- QTS 5.0.x and later
- QTS 4.5.4 and later
- QTS 4.3.6 and later
- QTS 4.3.4 and later
- QTS 4.3.3 and later
- QTS 4.2.6 and later
- QuTS hero h5.0.x and later
- QuTS hero h4.5.4 and later
- QuTScloud c5.0.x
Sonicwall patch

SSL Applicace SSLVPN SMA 1000 bug allows users to bypass authorization
| Summary | CVSS Score | Impacted Firmware | Fixed Firmware |
| Unauthenticated access control bypass | 8.2 (High) | 12.4.0 12.4.1 | 12.4.1-02994 |
| Use of hard-coded cryptographic key | 5.7 (Medium) | 12.4.0 12.4.1 | 12.4.1-02994 |
| URL redirection to an untrusted site (open redirection) | 6.1 (Medium) | 12.4.0 12.4.1 | 12.4.1-02994 |
“There are no temporary mitigations. SonicWall urges impacted customers to implement applicable patches as soon as possible,” the company says in a security advisory published this week.
Vulnerability Does not affect the following: SMA 1000 series running versions earlier than 12.4.0, SMA 100 series products, CMS, and remote access clients.
The security bugs impact the following SMA 1000 Series models: 6200, 6210, 7200, 7210, 8000v (ESX, KVM, Hyper-V, AWS, Azure).
CVE-2022-22282 is the most severe as it allows unauthenticated attackers to bypass authentication.
Most notable vulnerability: CVE-2022-1388 with CVSS 9.8 and internal assessment Critical due to the front-facing and lack of authentication checks potentially allowing an attacker to remotely execute code and attack the affected system
“This vulnerability may allow an unauthenticated attacker with network access to the BIG-IP system through the management port and/or self IP addresses to execute arbitrary system commands, create or delete files, or disable services,”
Zyxel Firewalls

Shadowserver Foundation reported seeing an increased attack number leveraging the CVE-2022-30525 recently discovered
The vulnerability was disclosed by Jacob Baines, a lead security researcher at Rapid7, that explain how the flaw can be leveraged in attacks.
More than 20000 Zyxel firewall affected are currently on the web (shodan results) requires login
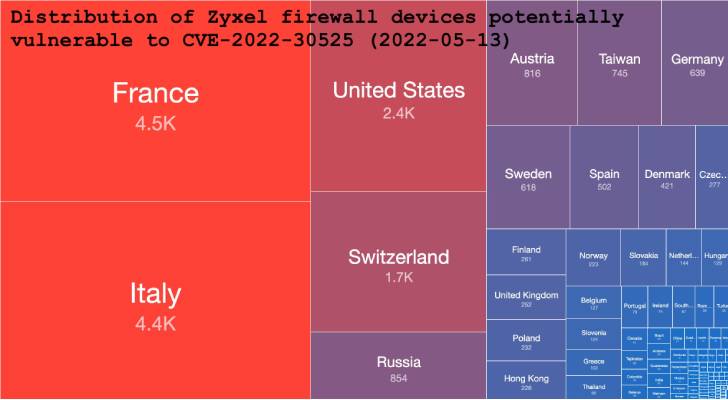
Metaexploit module has been added to test the vulnerability
“Commands are executed as the nobody user. This vulnerability is exploited through the /ztp/cgi-bin/handler URI and is the result of passing unsanitized attacker input into the os.system method in lib_wan_settings.py” –
Jacob Baines
The following models are affected
| Affected model | Affected firmware version | Patch availability |
|---|---|---|
| USG FLEX 100(W), 200, 500, 700 | ZLD V5.00 through ZLD V5.21 Patch 1 | ZLD V5.30 |
| USG FLEX 50(W) / USG20(W)-VPN | ZLD V5.10 through ZLD V5.21 Patch 1 | ZLD V5.30 |
| ATP series | ZLD V5.10 through ZLD V5.21 Patch 1 | ZLD V5.30 |
| VPN series | ZLD V4.60 through ZLD V5.21 Patch 1 | ZLD V5.30 |
Nvidia Card

Four vulnerabilities were addressed in the latest release. The fixes on the firmware have covered for Tesla, RTX/Quadro, NVS, Studio, and GeForce software products, covering driver branches R450, R470, and R510. Interestingly also covered support card with the latest release: GTX 600 and GTX 700 Kepler-series cards, whose support ended in October 2021.
- CVE-2022-28181 (CVSS v3 score: 8.5) – Out-of-bounds write in the kernel mode layer caused by a specially crafted shader sent over the network, potentially leading to code execution, denial of service, escalation of privileges, information disclosure, and data tampering.
- CVE-2022-28182 (CVSS v3 score: 8.5) – Flaw in DirectX11 user mode driver allowing an unauthorized attacker to send a specially crafted shared over the network and cause denial of service, escalation of privileges, information disclosure, and data tampering.
- CVE-2022-28183 (CVSS v3 score: 7.7) – Vulnerability in the kernel mode layer, where an unprivileged regular user can cause an out-of-bounds read, which may lead to denial of service and information disclosure.
- CVE-2022-28184 (CVSS v3 score: 7.1) – Vulnerability in the kernel mode layer (nvlddmkm.sys) handler for DxgkDdiEscape, where a regular unprivileged user can access administrator-privileged registers, which may lead to denial of service, information disclosure, and data tampering.
Cloud
Current Year Research on Vulnerabilities Discovered
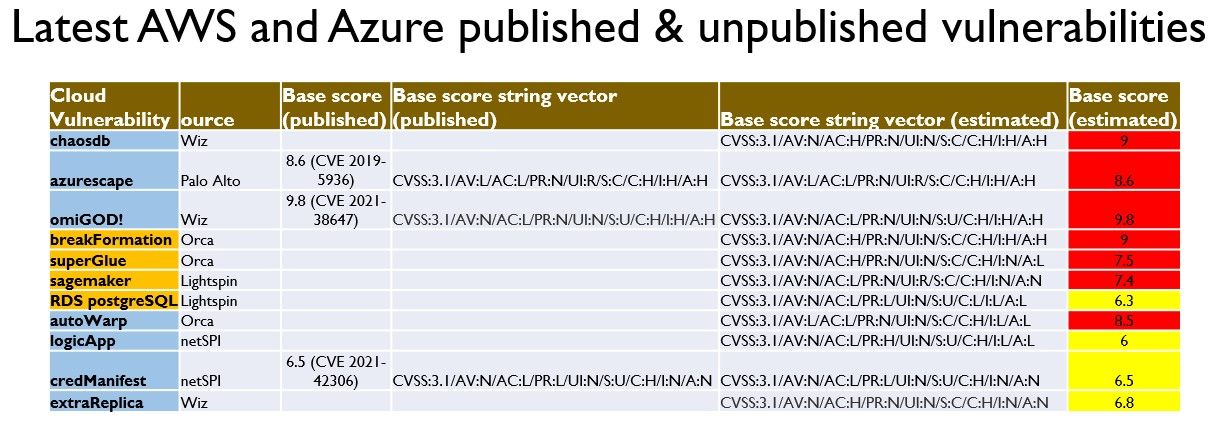
For the Deep dive on previous Cloud Vulnerabilities: https://phoenix.security/security-vulnerability-of-the-week-02-04-22/
sagemaker – Lightspin – CVSS 7.4

AWS SageMaker Jupyter Notebook
Lightspin researcher Gafnit Amiga found that an attacker can run any code on a victim’s SageMaker JupyterLab Notebook Instance across accounts.
The vulnerability has been already remediated
Using the access token, the attacker can read data from S3 buckets, create VPC endpoints and more actions that are allowed by the SageMaker execution role and the “AmazonSageMakerFullAccess” policy.
An attacker is able to use CSRF to send this POST request to install my malicious extension on the victim’s JupyterLab Instance.
The requirement to deploy the vulnerability is that the victim must be logged in the AWS account, and click on the malicious link to start the attack
For full vulnerability disclose: https://blog.lightspin.io/aws-sagemaker-notebook-takeover-vulnerability
RDS Postress SQL – Lightspin – CVSS 6.3

Amazon Web Services (AWS) resolved on 09 Mar 22 (disclosed date: 09Dec 2021) a vulnerability affecting Amazon Relational Database Service (RDS) that could lead to the exposure of internal credentials.
Another vulnerability was uncovered by the Lightspin’s Research Team. The team has obtained credentials to an internal AWS service by exploiting a local file read vulnerability on the RDS EC2 instance using the log_fdw extension. The internal AWS service was connected to AWS internal account, related to the RDS service.
The AWS team has disclosed that the patch was limited only to the recent RDS and Aurora PostgreSQL engines. AWS Team has reached out to all affected users
“No cross-customer or cross-cluster access was possible; however, highly privileged local database users who could exercise this issue could potentially have gained additional access to data hosted in their cluster or read files within the operating system of the underlying host running their database,” AWS explains.
For full vulnerability disclosure: https://blog.lightspin.io/aws-rds-critical-security-vulnerability
For AWS Bulletin: https://aws.amazon.com/security/security-bulletins/AWS-2022-004/