Weekly review of the top vulnerability issues of the week

This week there were mostly updates on existing flaws – Qnap, F5 discloses vulnerabilities,
This week features Raspberry Robin a windows malware work attacking QNAP, QNAP releasing bugfixes, F5 releasing Bugfixes, Github with more stringent controls on authentication
Appsec
NPM NPMJS with new CDN


The open-source project SheetJS aka XLSX has dropped support for NPM
The library was downloaded about 1.4 million times
The project’s maintainer suggests that the decision to pull out of the npm registry is based on the newly introduced two-factor requirements for top projects, GitHub’s abrupt decision-making, and ongoing ‘legal matters’ between SheetJS and npm
For the lates change on the CDN: https://github.com/SheetJS/sheetjs/commit/ed18acd63d7a5cd31527a36a9af54542cdfcfd30#diff-b335630551682c19a781afebcf4d07bf978fb1f8ac04c6bf87428ed5106870f5R219
The developer behind SheetJS quotes mostly the move of the 2FA
GitHub’s (see below) is actively enforcing the move to MFA (2 factor authentication) after recent incidents and previous year’s hijacking incidents that hit famous npm packages like ua-parser-js, coa and rc.
Github

Following last week’s announcement, Github is tightening security rules and posture
GitHub announced on 4/5/2022 that all users who contribute code on its platform (an estimated 83 million developers in total) will be required to enable two-factor authentication (2FA) on their accounts by the end of 2023.
Also to force stronger authentication due to recent issues with SMS based tokens: GitHub urges switching to security keys or TOTPs since threat actors can bypass or steal SMS 2FA auth tokens.
The actions come after the recently discovered breach. The organization continues to issue the following advice despite the fact that very little user base was affected
- Review all your private repositories for secrets or credentials stored in them. There are several tools that can help with this task, such as GitHub secret scanning and trufflehog.
- Review the OAuth applications that you’ve authorized for your personal account or that are authorized to access your organization and remove anything that’s no longer needed.
- Follow GitHub’s guidelines for hardening the security posture of your GitHub organization.
- Review your account activity, personal access tokens, OAuth apps, and SSH keys for any activity or changes that may have come from the attacker.
- Additional questions should be directed to GitHub Support.
- Review all your private repositories for secrets or credentials stored in them. There are several tools that can help with this task, such as GitHub secret scanning and trufflehog.
- Review the OAuth applications that you’ve authorized for your personal account or that are authorized to access your organization and remove anything that’s no longer needed.
- Follow GitHub’s guidelines for hardening the security posture of your GitHub organization.
- Review your account activity, personal access tokens, OAuth apps, and SSH keys for any activity or changes that may have come from the attacker.
- Additional questions should be directed to GitHub Support.
For the Full report on Git: https://phoenix.security/security-vulnerability-of-the-week-02-04-22/
INFRA/Network
Windows – Raspberry Robin Vulnerability
A new Windows malware with worm-like affects Windows targeting QNAP. the malware has worm-like capabilities is propagated by means of removable USB devices.
Attack chains pertaining to Raspberry Robin start with connecting an infected USB drive to a Windows machine. Present within the device is the worm payload, which appears as a .LNK shortcut file to a legitimate folder.
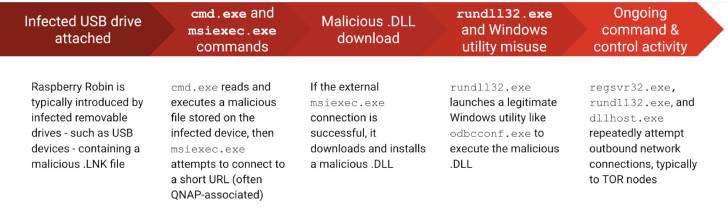
The worm then takes care of spawning a new process using cmd.exe to read and execute a malicious file stored on the external drive.
To monitor attacks: Raspberry Robin detections so far is the presence of outbound C2 contact involving the processes regsvr32.exe, rundll32.exe, and dllhost.exe to IP addresses associated with Tor nodes.
For more info: https://thehackernews.com/2022/05/researchers-warn-of-raspberry-robin.html
QNAP
Tracked as CVE-2022-27588 (CVSS score: 9.8), the vulnerability has been addressed in QVR 5.1.6 build 20220401 and later.
CVE-2022-23121 and other were discovered by NCC Group EDG team at Pwn2Own
“A vulnerability has been reported to affect QNAP VS Series NVR running QVR,” QNAP said in an advisory. “If exploited, this vulnerability allows remote attackers to run arbitrary commands.”
The following Vulnerabilities were discovered
- CVE-2021-38693 (CVSS score: 5.3) – A path traversal vulnerability in the httpd affecting QNAP devices running QTS, QuTS hero, QuTScloud, and QVR Pro Appliance, leading to information disclosure
- CVE-2021-44051 (CVSS score: 8.8) – A command injection vulnerability in QNAP devices running QTS, QuTS hero, and QuTScloud, resulting in arbitrary command execution
- CVE-2021-44052 (CVSS score: 6.5) – An improper link resolution before file access (“link following”) vulnerability in QNAP devices running QTS, QuTS hero, and QuTScloud, allowing attackers to read/write files in arbitrary file locations
- CVE-2021-44053 (CVSS score: 5.7) – A cross-site scripting (XSS) vulnerability in QNAP devices running QTS, QuTS hero, and QuTScloud, leading to code injection
- CVE-2021-44054 (CVSS score: 4.3) – An open redirect vulnerability in QNAP devices running QTS, QuTS hero, and QuTScloud, making it possible to redirect users to a rogue web pages
- CVE-2021-44055 (CVSS score: 5.3) – A missing authorization vulnerability in QNAP devices running Video Station, allowing attackers to access data or perform unauthorized actions
- CVE-2021-44056 (CVSS score: 7.1) – An improper authentication vulnerability in QNAP devices running Video Station, leading to system compromise
- CVE-2021-44057 (CVSS score: 7.1) – An improper authentication vulnerability in QNAP devices running Photo Station, leading to system compromise
NCC Group’s EDG team members exploited one of these security flaws, tracked as CVE-2022-23121 and rated with a 9.8/10 severity score
Three of the other bugs QNAP warned its customers about also received 9.8/10 severity ratings (i.e., CVE-2022-23125, CVE-2022-23122, CVE-2022-0194)
- QTS 5.0.x and later
- QTS 4.5.4 and later
- QTS 4.3.6 and later
- QTS 4.3.4 and later
- QTS 4.3.3 and later
- QTS 4.2.6 and later
- QuTS hero h5.0.x and later
- QuTS hero h4.5.4 and later
- QuTScloud c5.0.x
F5

F5 on Wednesday released patches to contain 43 bugs spanning its products.
43 issues addressed, one is rated Critical, 17 are rated High, 24 are rated Medium, and one is rated low in severity.
Most notable vulnerability: CVE-2022-1388 with CVSS 9.8 and internal assessment Critical due to the front-facing and lack of authentication checks potentially allowing attacker to remotely execute code and attack affected system
“This vulnerability may allow an unauthenticated attacker with network access to the BIG-IP system through the management port and/or self IP addresses to execute arbitrary system commands, create or delete files, or disable services,”
Affected Products: Big IP with the following version
- 16.1.0 – 16.1.2
- 15.1.0 – 15.1.5
- 14.1.0 – 14.1.4
- 13.1.0 – 13.1.4
- 12.1.0 – 12.1.6
- 11.6.1 – 11.6.5
- 16.1.0 – 16.1.2
- 15.1.0 – 15.1.5
- 14.1.0 – 14.1.4
- 13.1.0 – 13.1.4
- 12.1.0 – 12.1.6
- 11.6.1 – 11.6.5
Trend

Trend Micro antivirus has fixed a false positive affecting its Apex One endpoint security solution that caused Microsoft Edge updates to be tagged as malware and the Windows registry to be incorrectly modified.
the false positive has been raised to multiple forums and social media
As users further revealed, the Trend Micro Apex One flagged the browser updates as Virus/Malware: TROJ_FRS.VSNTE222 and Virus/Malware: TSC_GENCLEAN.
For the full news refer to:
Cloud
Heroku

Heroku platform owned by Salesforce has performed a round of forced password resets in response to a security incident from last month.
“As part of our efforts to enhance our security and in response to an incident published on status.heroku.com, we wanted to inform you that we will begin resetting user account passwords on May 4, 2022,” read the email sent to Heroku customers.
The breach was linked to a recent breach of Github repositories and the attacker leveraging the exposed credentials.
from Hacker News reader “There was certainly a breach three weeks ago that they seem to have been investigating since. I am, like the commenter above, not filled with confidence about their statement, mostly because of the total lack of transparency so far”
We covered Github breach: https://phoenix.security/vulnerability-weekly/?playlist=728882e&video=1e6673c
The latest incident report from Heroku: https://status.heroku.com/incidents/2413
Google Docs crashes

A recent bug discovered on May 6 in Google Docs is causing it to crash when a series of words are typed into a document opened with the online word processor.
A Google Docs user, Pat Needham brought up the issue on Google Docs Editors Help forum.
Google Docs crashes at the sight of “And. And. And. And. And.” when the “Show grammar suggestion” is turned on.
“It’s case-sensitive. So trying with ‘and. and. And. and. And.’ doesn’t cause it to crash.”
The bug has been resolved: May 6th, 2022 04:56 AM ET:BleepingComputer where the first news was reported was no longer able to reproduce the bug. We continue to await an official response from Google on the matter.
Current Year Research on Vulnerabilities Discovered
For the Deep dive on previous Cloud Vulnerabilities: https://phoenix.security/security-vulnerability-of-the-week-02-04-22/
Hotpatch of AWS Log4J

CVE IDs: CVE-2021-3100, CVE-2021-3101, CVE-2022-0070, CVE-2022-0071
Amazon as per December released several version of AMI with patched version of Log4J.
Security Researchers from palo alto have disclosed Security researchers recently reported issues within the hotpatch released in December, and the associated OCI hooks for Bottlerocket (“Hotdog”). We have addressed these issues within a new version of the hotpatch, and a new version of Hotdog.
The latest package names and versions of the hotpatch for Amazon Linux and Amazon Linux 2 are as follows:
- Amazon Linux: log4j-cve-2021-44228-hotpatch-1.1-16.amzn1
- Amazon Linux 2: log4j-cve-2021-44228-hotpatch-1.1-16.amzn2
Full Post: https://aws.amazon.com/security/security-bulletins/AWS-2022-006/
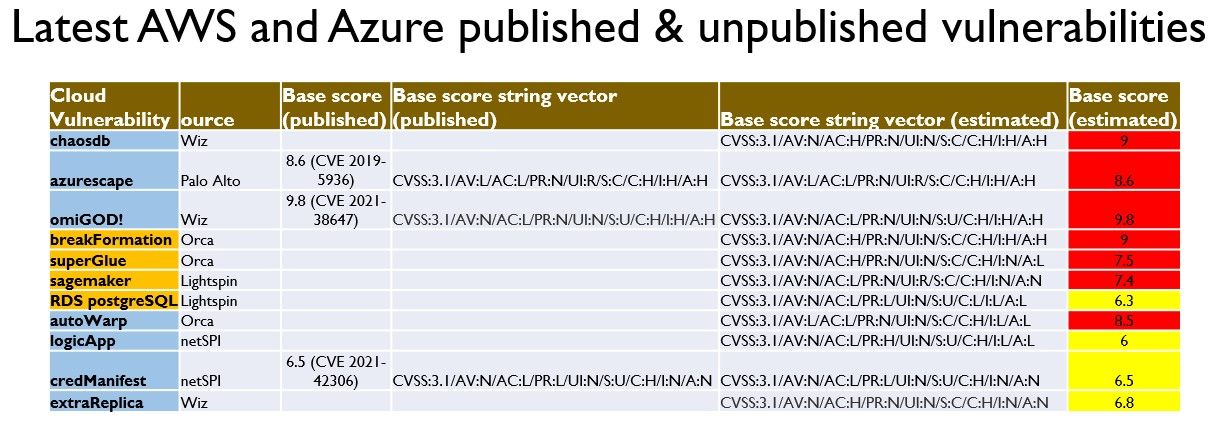
Superglue – Orca –
Orca Security team did discover on Jan 2022 a critical security issue in the AWS Glue service that could allow an actor to create resources and access data of other AWS Glue customers.
AWS Glue is a serverless data integration service that makes it easy to discover, prepare, and combine data for analytics, machine learning, and application development. During our research, we were able to identify a feature in AWS Glue that could be exploited to obtain credentials to a role within the AWS service’s own account, which provided us full access to the internal service API.
Bulletin: https://aws.amazon.com/security/security-bulletins/AWS-2022-002/
the orca security team were able to
- Assume roles in AWS customer accounts that are trusted by the Glue service. In every account that uses Glue, there’s at least one role of this kind.
- Query and modify AWS Glue service-related resources in a region. This includes but is not limited to metadata for: Glue jobs, dev endpoints, workflows, crawlers and triggers.
For more info: https://orca.security/resources/blog/aws-glue-vulnerability
sagemaker – Lightspin – CVSS 7.4
RDS Postress SQL – Lightspin – CVSS 6.3
AutoWrap – Orca – CVSS 8.5
logicApp – NetSPI – CVSS 6
credManifest – NetSPI – CVSS 6.5 – CVE 2021-42306
extraReplica – Wiz – CVSS 6.8
Bonus
XBOX Live Down

For all the gamers on May 6th Microsoft says the Xbox Live services were currently down in a major outage, impacting customers worldwide and preventing them from launching or buying games.
The service was down for two and more hours according to https://downdetector.com/status/xbox-live/